Insider Threat Plan Template
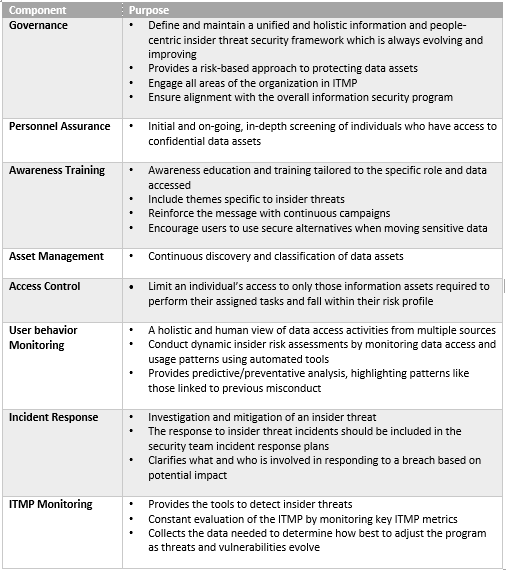
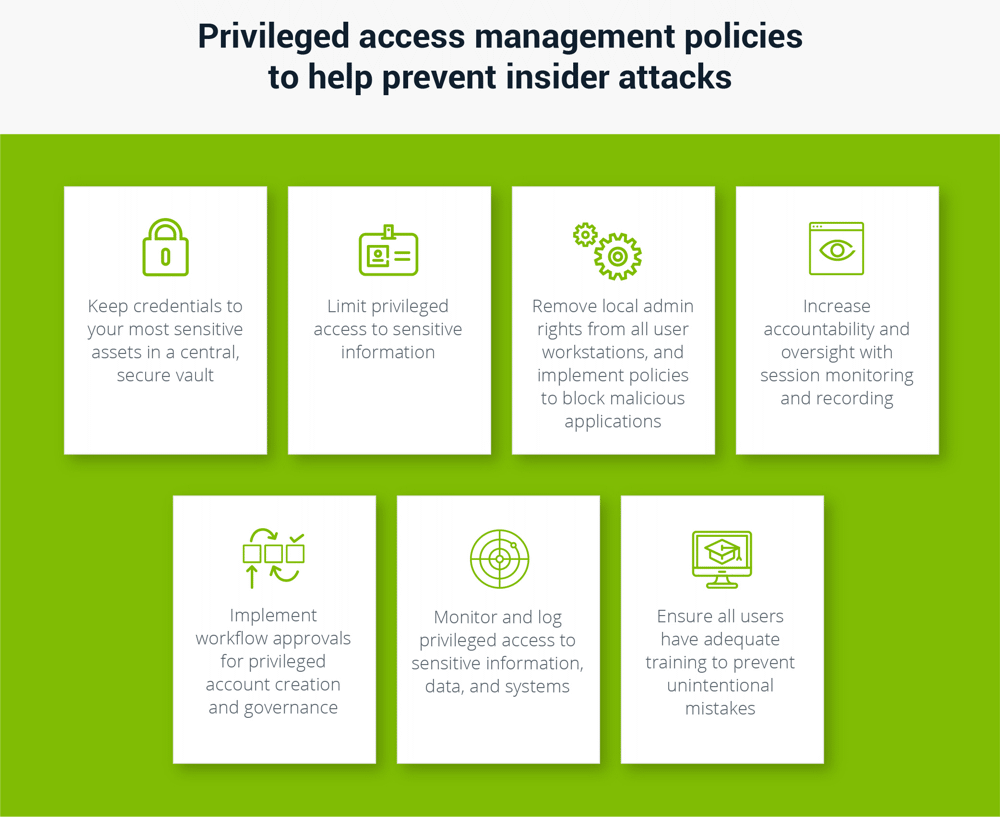
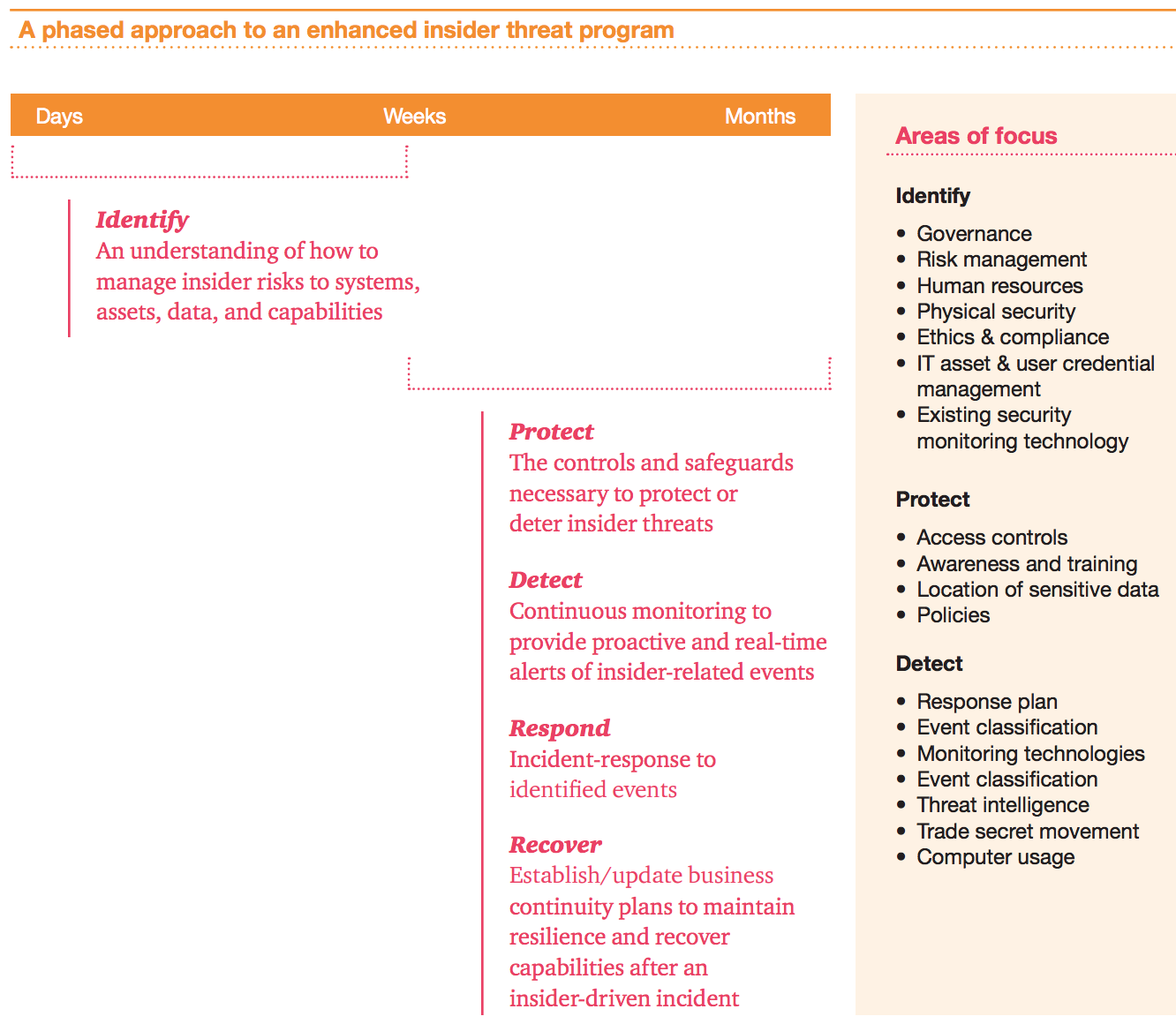
Insider Threat Plan Template - Guy bunker from clearswift states that:. Web 1to establish and maintain an insider threat program to detect, deter and mitigate insider threats. Web the first step in creating this plan is to accept the reality and recognize that an incident response plan is a business imperative. Web june 9, 2021 the diplomatic security service manages/administers the department of state’s insider threat program to protect the department, its people,. On cisa.gov, visitors will find. Web it is not a template. Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their critical assets against insider threats. More industry insider threat information and resources. Web september is national insider threat awareness month, but business owners must always keep insider threat in mind. Every single business owner risks the.
Insider Threat Mitigation
Guy bunker from clearswift states that:. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly, to do harm to the department's mission,. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national security. Web communications plan.
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
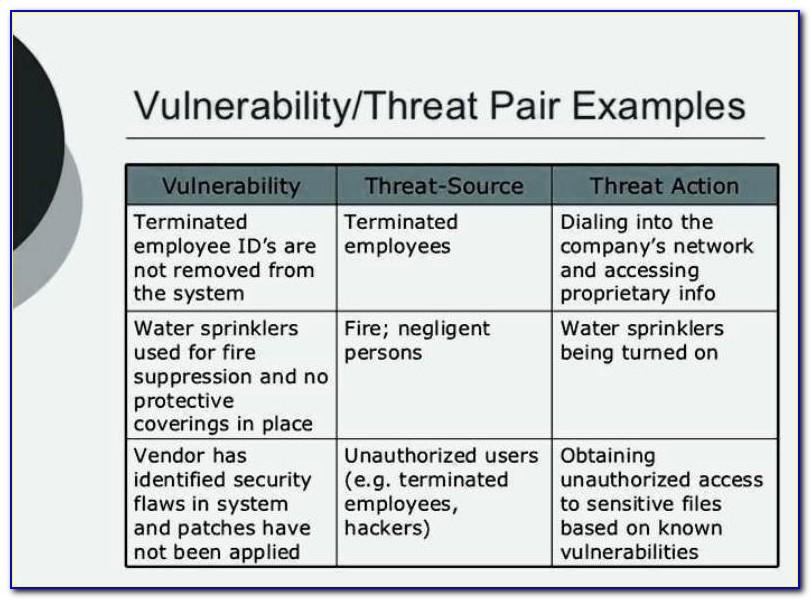
Web it is not a template. Defining the threat, detecting and identifying the threat, assessing the threat, and managing the threat. Specifically, the program must gather, integrate, and report relevant and. On cisa.gov, visitors will find. Web september is national insider threat awareness month, but business owners must always keep insider threat in mind.
Building an Insider Threat Management Program Divurgent
Web september is national insider threat awareness month, but business owners must always keep insider threat in mind. Web an insider threat program is “a coordinated group of capabilities under centralized management that is organized to detect and prevent the unauthorized. Web this toolkit will quickly point you to the resources you need to help you perform your role in.
Insider Threat Plan Template Master of Documents
Web partners can use cteps to initiate discussions within their organizations about their ability to address a variety of threat scenarios. There is no foolproof formula for identifying or predicting an insider threat; Web cisa defines insider threat as the threat that an insider will use their authorized access, wittingly or unwittingly, to do harm to the department’s mission, resources,.
How to Prevent Insider Threats Case Studies, Examples, Types
However, most maligned insiders exhibit risky. Web an insider threat program is “a coordinated group of capabilities under centralized management that is organized to detect and prevent the unauthorized. Web june 9, 2021 the diplomatic security service manages/administers the department of state’s insider threat program to protect the department, its people,. Web partners can use cteps to initiate discussions within.
Insider Threat Report SC Report Template Tenable®
Guy bunker from clearswift states that:. Web september is national insider threat awareness month, but business owners must always keep insider threat in mind. On cisa.gov, visitors will find. More industry insider threat information and resources. Each package is customizable and includes.
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
Guy bunker from clearswift states that:. Web an incident response plan or ir plan is a set of tools and processes startups can leverage to detect, eliminate and recover from cyber threats. Web the first step in creating this plan is to accept the reality and recognize that an incident response plan is a business imperative. Web cisa defines insider.
Example Insider Threat Program Organizational Structure and Data
Guy bunker from clearswift states that:. Each package is customizable and includes. Web communications plan & messaging packet dod insider threat program, office of the under secretary of defense for intelligence and security ousd (i&s) 1. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Web an insider threat program is.
Insider Threat Program What It Is & Checklist for Building One Ekran
Web how can you identify an insider threat? Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly, to do harm to the department's mission,. Web partners can use cteps to initiate discussions within their organizations about their ability to address a variety of threat scenarios. Web.
building an insider threat program Risk Management Monitor
Guy bunker from clearswift states that:. Web partners can use cteps to initiate discussions within their organizations about their ability to address a variety of threat scenarios. Specifically, the program must gather, integrate, and report relevant and. Web communications plan & messaging packet dod insider threat program, office of the under secretary of defense for intelligence and security ousd (i&s).
Web september is national insider threat awareness month, but business owners must always keep insider threat in mind. There is no foolproof formula for identifying or predicting an insider threat; Web the first step in creating this plan is to accept the reality and recognize that an incident response plan is a business imperative. Defining the threat, detecting and identifying the threat, assessing the threat, and managing the threat. Web dcsa continues to assess compliance with minimum insider threat requirements, which provide the basic elements necessary to establish a fully functional insider threat. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national security. Web an “insider threat” is now defined as the threat that an insider will use his or her authorized access, wittingly or unwittingly, to do harm to the department's mission,. Web it is not a template. Each package is customizable and includes. However, most maligned insiders exhibit risky. Web partners can use cteps to initiate discussions within their organizations about their ability to address a variety of threat scenarios. Insider threat indicators in uam june 2023, 7. Every single business owner risks the. Web an incident response plan or ir plan is a set of tools and processes startups can leverage to detect, eliminate and recover from cyber threats. On cisa.gov, visitors will find. Web june 9, 2021 the diplomatic security service manages/administers the department of state’s insider threat program to protect the department, its people,. Web how can you identify an insider threat? Web ey’s insider threat program framework helps organizations develop an integrated risk management program to protect their critical assets against insider threats. Web 1to establish and maintain an insider threat program to detect, deter and mitigate insider threats.