Insider Threat Policy Template
Insider Threat Policy Template - Web insider threat roadmap 2020 administrator’s message am proud to present the transportation security administration’s (tsa) insider threat roadmap. Web the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: Web a current or former employee, contractor, or business partner who has or had authorized access to the organization’s network, systems, or data. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Defining the threat, detecting and identifying the threat, assessing the threat, and managing the threat. More industry insider threat information and resources. In november 2012, the president issued the national insider threat policy and the minimum. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; Attorneys steal and destroy data from their law firm. Web an insider threat is when a current or former employee, contractor or business partner, who has or had authorized access to an organization’s network systems, data or premises,.
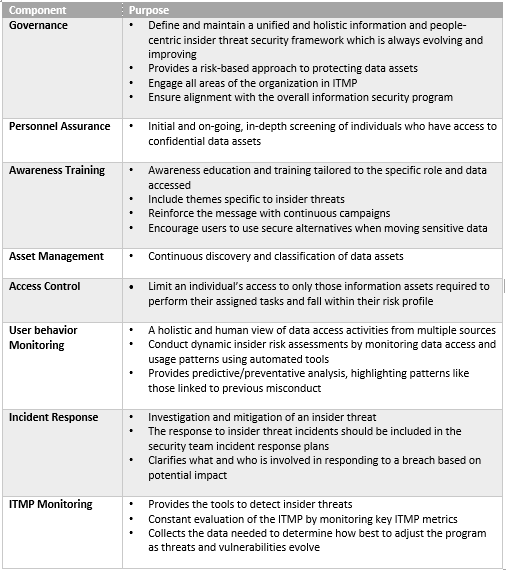
Building an Insider Threat Management Program Divurgent
Attorneys steal and destroy data from their law firm. Web information to establish insider threat detection and prevention programs. Insider threat indicators in uam june 2023, 7. Web a current or former employee, contractor, or business partner who has or had authorized access to the organization’s network, systems, or data. On cisa.gov, visitors will find.
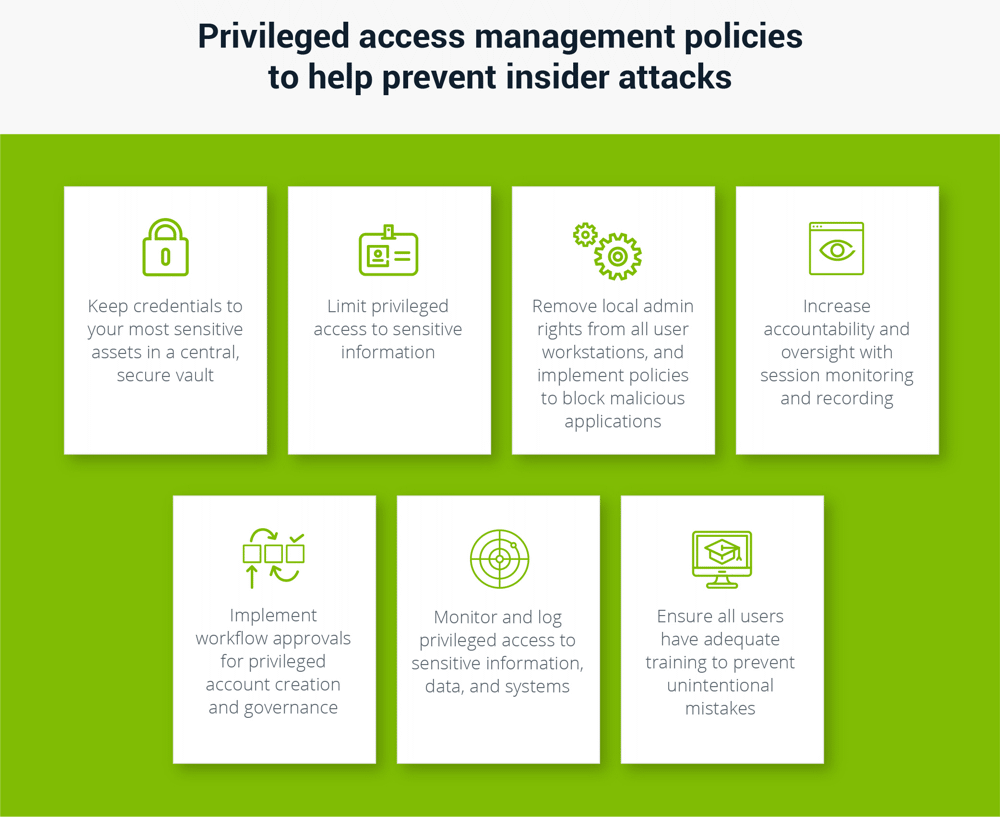
How to Prevent Insider Threats Case Studies, Examples, Types (2022)
Web the new definitions of “insider threat” and “insider” expands upon the definitions found in eo 13587 and the national insider threat policy and minimum standards for executive. On cisa.gov, visitors will find. Web 10 steps to create an efficient insider threat program. In november 2012, the president issued the national insider threat policy and the minimum. Web an insider.
Insider Threat Mitigation
Web a current or former employee, contractor, or business partner who has or had authorized access to the organization’s network, systems, or data. Web the insider threat mission is a dynamic effort requiring constant evaluation, fresh perspectives, and updated approaches. Web an insider threat is when a current or former employee, contractor or business partner, who has or had authorized.
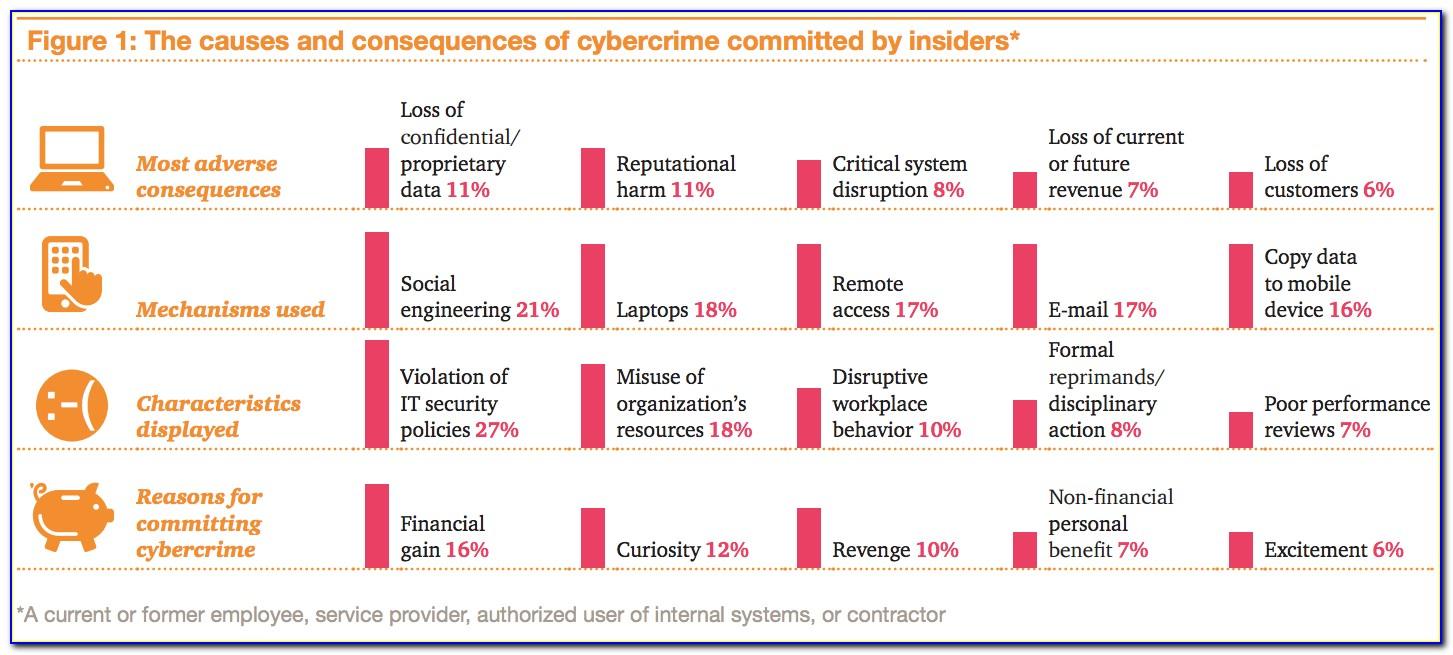
Protecting against insider risks in an uncertain environment
Web the new definitions of “insider threat” and “insider” expands upon the definitions found in eo 13587 and the national insider threat policy and minimum standards for executive. Insider threat indicators in uam june 2023, 7. Examples of an insider may. Attorneys steal and destroy data from their law firm. On cisa.gov, visitors will find.
Security Insider Threat Safety Central
In november 2012, the president issued the national insider threat policy and the minimum. Web the new definitions of “insider threat” and “insider” expands upon the definitions found in eo 13587 and the national insider threat policy and minimum standards for executive. Establishes policy and assigns responsibilities within dod to develop and maintain an insider threat program to comply with.
Breaking White House Announces “Insider Threat” Policy Archives
Examples of an insider may. Attorneys steal and destroy data from their law firm. Web the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: In november 2012, the president issued the national insider threat policy and the minimum. Insider threat indicators in uam june 2023, 7.
Insider Threat Program Template Template Resume Examples QBD3E4RYOX
Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national security. Web the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: Establishes policy and assigns responsibilities within dod to develop and maintain an insider threat program to comply with the requirements and minimum..
Cybersecurity HQ An Insider Attack on the Industry
In november 2012, the president issued the national insider threat policy and the minimum. Web to help understand the gravity of the insider threat factor, let’s look at some examples. Web information to establish insider threat detection and prevention programs. Establishes policy and assigns responsibilities within dod to develop and maintain an insider threat program to comply with the requirements.
Insider Threat Report SC Report Template Tenable®
Establishes policy and assigns responsibilities within dod to develop and maintain an insider threat program to comply with the requirements and minimum. This plan establishes policy and assigns responsibilities for the insider threat program (itp). Web the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: Examples of an insider may. Web the new.
Insider Threat Plan Template Master of Documents
In november 2012, the president issued the national insider threat policy and the minimum. Web the insider threat mission is a dynamic effort requiring constant evaluation, fresh perspectives, and updated approaches. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web national insider threat policy the.
Establishes policy and assigns responsibilities within dod to develop and maintain an insider threat program to comply with the requirements and minimum. Web the insider threat mitigation guide provides comprehensive information to help federal, state, local, tribal, and territorial governments; This plan establishes policy and assigns responsibilities for the insider threat program (itp). On cisa.gov, visitors will find. Web the insider threat mission is a dynamic effort requiring constant evaluation, fresh perspectives, and updated approaches. An insider threat is a type of cyberattack originating from an individual who works for an organization or has authorized access to its networks or. Web the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: Web national insider threat policy the national insider threat policy aims to strengthen the protection and safeguarding of classified information by: Web the new definitions of “insider threat” and “insider” expands upon the definitions found in eo 13587 and the national insider threat policy and minimum standards for executive. Web this toolkit will quickly point you to the resources you need to help you perform your role in the insider threat field. Web an insider threat is when a current or former employee, contractor or business partner, who has or had authorized access to an organization’s network systems, data or premises,. Attorneys steal and destroy data from their law firm. Web 10 steps to create an efficient insider threat program. Web a current or former employee, contractor, or business partner who has or had authorized access to the organization’s network, systems, or data. Examples of an insider may. Web to help understand the gravity of the insider threat factor, let’s look at some examples. Web cisa defines insider threat as the threat that an insider will use their authorized access, wittingly or unwittingly, to do harm to the department’s mission, resources, personnel,. In november 2012, the president issued the national insider threat policy and the minimum. Insider threat indicators in uam june 2023, 7. Web insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national security.