Nist Continuous Monitoring Plan Template
Nist Continuous Monitoring Plan Template - It can be used as documented or. Web nist has published nistir 8212, an information security continuous monitoring program assessment, and the iscmax tool that implements the iscm. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program assessment that can be used to evaluate. Web the world’s leading cybersecurity guidance is getting its first complete makeover since its release nearly a decade ago. Web nist information system contingency plan template type form & templates nist information system contingency plan templates for high, moderate,. Web information security continuous monitoring (iscm) is defined as maintaining ongoing awareness of information security, vulnerabilities, and threats to support organizational. Web abstract the purpose of this guideline is to assist organizations in the development of a continuous monitoring strategy and the implementation of a. Web new new new and after we build it right. Web the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to increase visibility into assets and awareness of. The templates can be customized and used as an outline of an organizational.
DFARS Archives CKSS Cybersecurity Solutions
Web the world’s leading cybersecurity guidance is getting its first complete makeover since its release nearly a decade ago. Web nistir 8212, an information security continuous monitoring program assessment, provides an operational approach to the assessment of an organization’s. An information security continuous monitoring program assessment, provides an. Illustrates an excerpt of a notional action plan template, as described in.
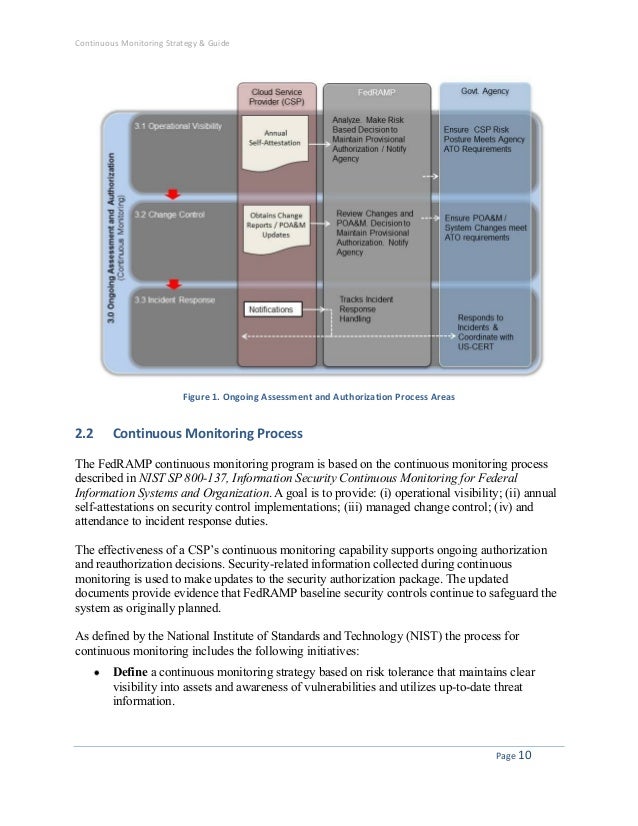
Continuous monitoring strategy_guide_072712
The templates can be customized and used as an outline of an organizational. It can be used as documented or. Web nist information system contingency plan template type form & templates nist information system contingency plan templates for high, moderate,. Web information security continuous monitoring (iscm) is defined as maintaining ongoing awareness of information security, vulnerabilities, and threats to support.
NIST Cybersecurity Framework Cybersecurity framework, Cyber security
Web nist information system contingency plan template type form & templates nist information system contingency plan templates for high, moderate,. Web the world’s leading cybersecurity guidance is getting its first complete makeover since its release nearly a decade ago. Fedramp updated the plan of actions and milestones (poa&m) template to include two new columns. Web new new new and after.
Nist 800 Risk Assessment Template Nist 800 Risk Assessment Template
Web notional action plan template 802 table 2. The templates can be customized and used as an outline of an organizational. Web nist has published nistir 8212, an information security continuous monitoring program assessment, and the iscmax tool that implements the iscm. Web continuous monitoring programs facilitate ongoing awareness of threats, vulnerabilities, and information security to support organizational risk management.
Nist Security Plan Template Template 1 Resume Examples MZe12Xo3jx
Web this publication describes an approach for the development of information security continuous monitoring (iscm) program assessments that can be used to. Illustrates an excerpt of a notional action plan template, as described in section 3.1. After considering more than a year’s. Web as defined by nist, the process for continuous monitoring includes the following initiatives: Web notional action plan.
NIST Revises Guide on Security Controls Security assessment, Business
It was developed directly from nist guidance and is applicable to any organization, public or private. After considering more than a year’s. Web october 01, 2020 draft nist interagency report (nistir) 8212 , iscma: Web continuous monitoring programs facilitate ongoing awareness of threats, vulnerabilities, and information security to support organizational risk management decisions. Web continuous monitoring (iscm) program.
Rmf Continuous Monitoring Plan Template Master of Documents
It can be used as documented or. Web the monitoring program, revising the continuous monitoring strategy and maturing measurement capabilities to increase visibility into assets and awareness of. Web the world’s leading cybersecurity guidance is getting its first complete makeover since its release nearly a decade ago. Web june 28 | 2022. Web abstract the purpose of this guideline is.
RMF Continuous Monitoring (When You’re Out of Bandwidth)
Web continuous monitoring (iscm) program. Web nistir 8212, an information security continuous monitoring program assessment, provides an operational approach to the assessment of an organization’s. Web new new new and after we build it right. Web the policy templates are provided courtesy of the state of new york and the state of california. Illustrates an excerpt of a notional action.
TEMPLATE Continuous Monitoring Plan (ConMon) ⋆ The Cyber Sentinel
Web new new new and after we build it right. Web continuous monitoring (iscm) program. The templates can be customized and used as an outline of an organizational. Web continuous monitoring pdf continuous monitoring escalation process this document explains the actions taken when a service provider fails to maintain an adequate. Web the purpose of this guideline is to assist.
NIST SP 800137 Information security continuous monitoring (ISCM)
Fedramp updated the plan of actions and milestones (poa&m) template to include two new columns. After considering more than a year’s. § define a continuous monitoring strategy based on risk tolerance. This publication describes an example methodology for assessing an organization's information security continuous monitoring (iscm) program. Web the world’s leading cybersecurity guidance is getting its first complete makeover since.
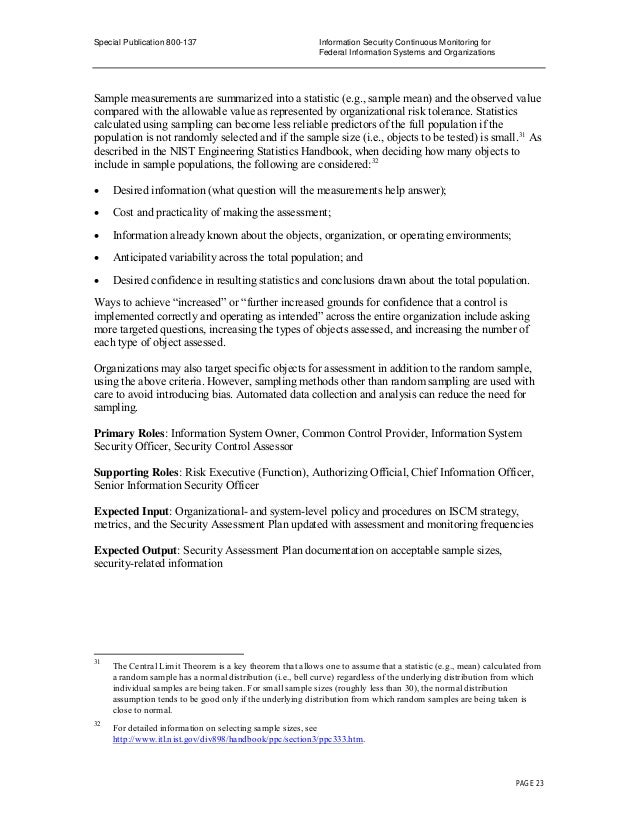
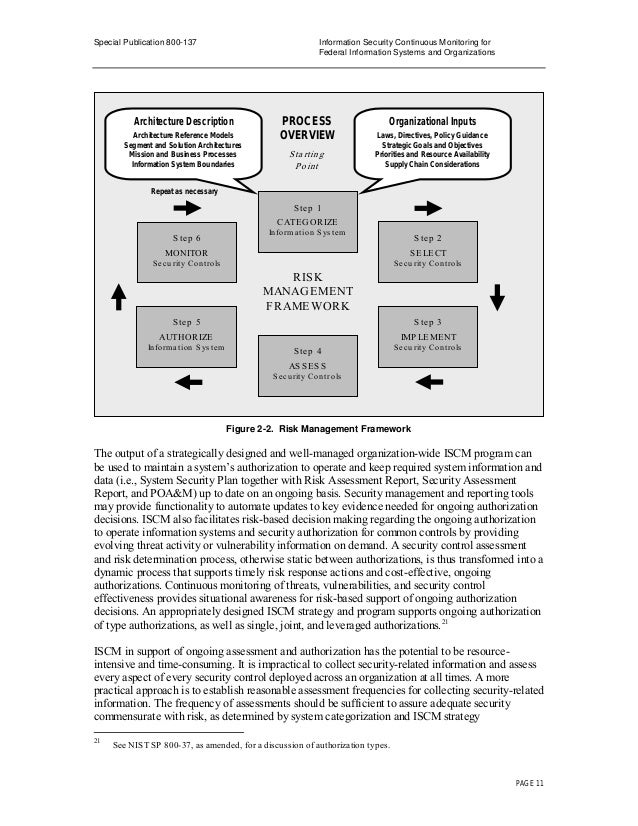
After considering more than a year’s. Illustrates an excerpt of a notional action plan template, as described in section 3.1. Web nist information system contingency plan template type form & templates nist information system contingency plan templates for high, moderate,. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program assessments that can be used to. Web as defined by nist, the process for continuous monitoring includes the following initiatives: It was developed directly from nist guidance and is applicable to any organization, public or private. Web abstract the purpose of this guideline is to assist organizations in the development of a continuous monitoring strategy and the implementation of a. Web october 01, 2020 draft nist interagency report (nistir) 8212 , iscma: Web abstract this publication describes an example methodology for assessing an organization’s information security continuous monitoring (iscm) program. Web the world’s leading cybersecurity guidance is getting its first complete makeover since its release nearly a decade ago. Web continuous monitoring (iscm) program. Web this publication describes an approach for the development of information security continuous monitoring (iscm) program assessment that can be used to evaluate. Web june 28 | 2022. Web nist has published nistir 8212, an information security continuous monitoring program assessment, and the iscmax tool that implements the iscm. It can be used as documented or. This publication describes an example methodology for assessing an organization's information security continuous monitoring (iscm) program. Web the purpose of this guideline is to assist organizations in the development of a continuous monitoring strategy and the implementation of a continuous monitorin. Web continuous monitoring programs facilitate ongoing awareness of threats, vulnerabilities, and information security to support organizational risk management decisions. Web continuous monitoring pdf continuous monitoring escalation process this document explains the actions taken when a service provider fails to maintain an adequate. An information security continuous monitoring program assessment, provides an.