Ransomware Policy Template
Ransomware Policy Template - After the initial infection, the ransomware attempts to spread to shared storage drives and other accessible systems. Web the policy should specify the parameters to be considered, including the cost of the ransom vs. Web fortunately, organizations can take steps to prepare for ransomware attacks. Web a ransomware incident response plan may be the difference between surviving an attack and shuttering operations. You must have at least one app connected using app connectors. Web new blackcat ransomware variant adopts advanced impacket and remcom tools. Malicious actors then demand ransom in exchange for decryption. Here are nist resources that can help you with ransomware protection and response. It’s listed as ransomware policy with a little new sign after it. Ransomware extortion and destructive attacks only work when all legitimate access to.
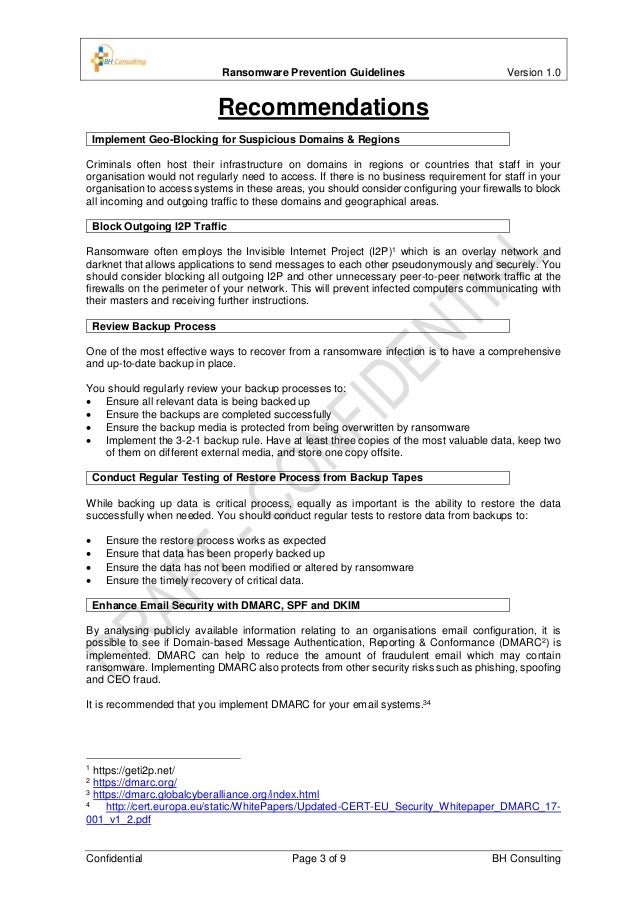
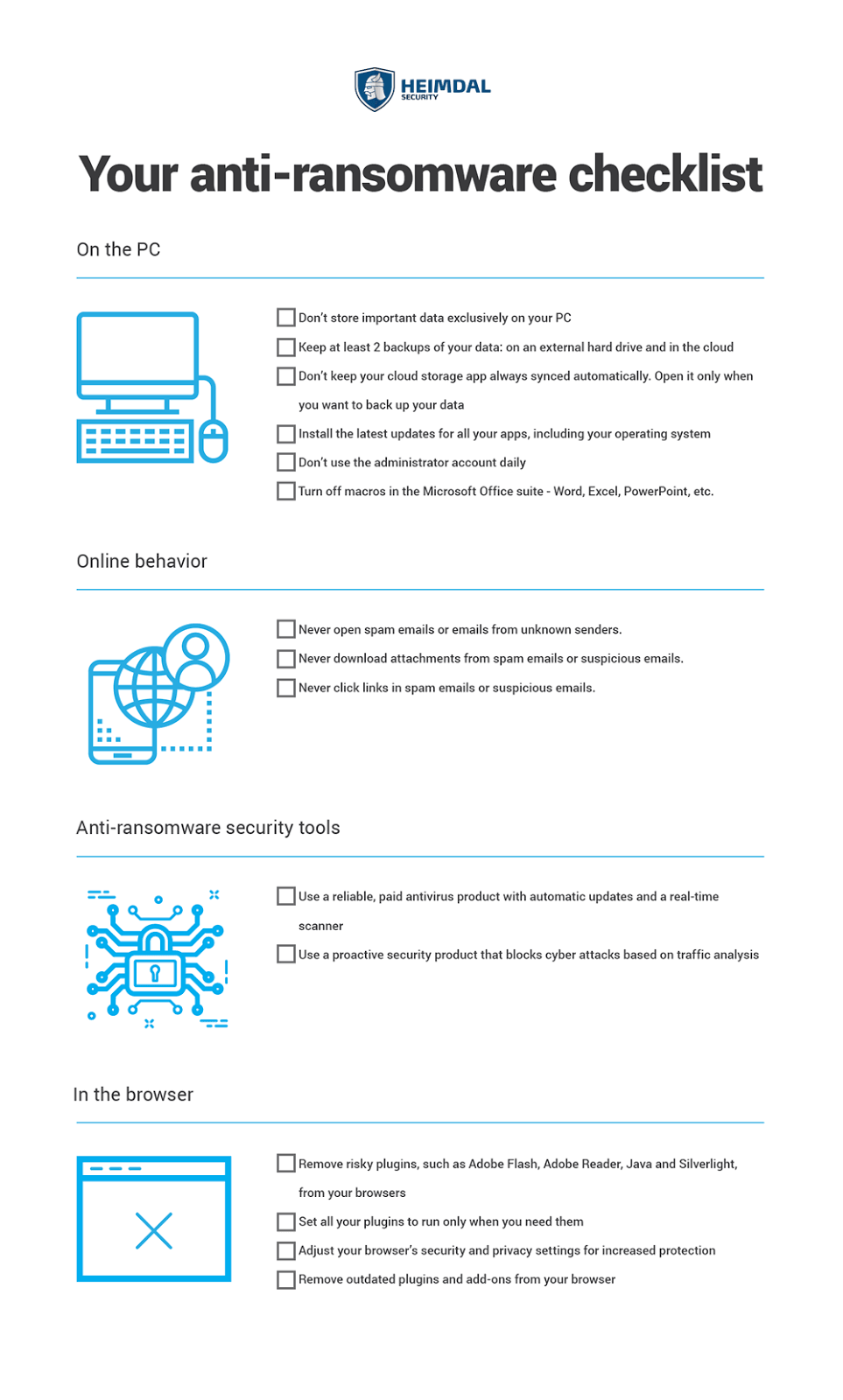
Ransomware Prevention Guide
Web so you may need a ransomware policy. You must have at least one app connected using app connectors. Here are additional resources from nist and partner federal agencies to help you protect against and respond to ransomware attacks : Web you must implement data protection to ensure rapid and reliable recovery from a ransomware attack and to block some.
Hybrid Ransomware Policy Commercial Crime Concepts
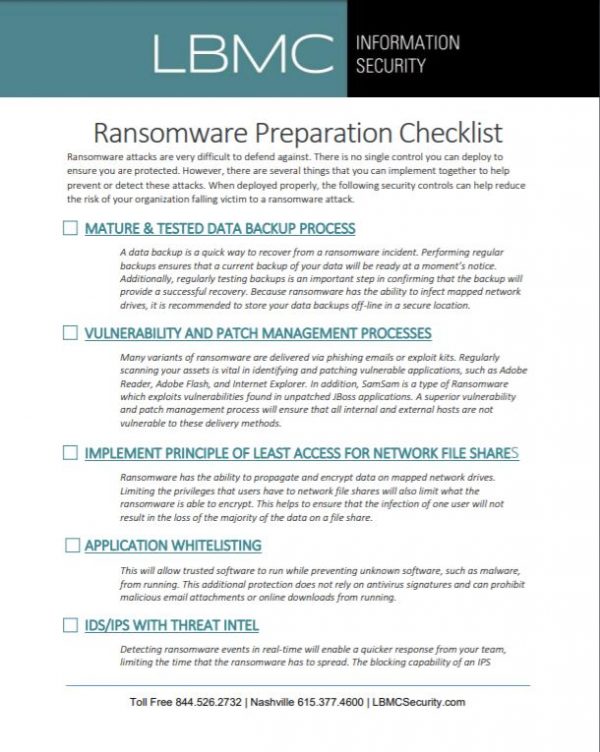
Read key planning steps, and download a free template to get started. Preparing your organization for ransomware attacks. This includes protecting data and devices from ransomware and being ready to respond to any ransomware attacks that succeed. Nuspire's q2 2023 cyber threat report shows rapid growth of cl0p ransomware gang. The malicious cyber actor holds systems or data hostage until.
Overview of threat protection scenario Microsoft Docs
Web create the policy. Web ransomware ppt templates,google slides download over 6,300+ complete free templates in high resolution. Web get ahead of your 2023 security goals. Malicious actors then demand ransom in exchange for decryption. Web so you may need a ransomware policy.
Defending Against Ransomware Prevention, Protection, Removal
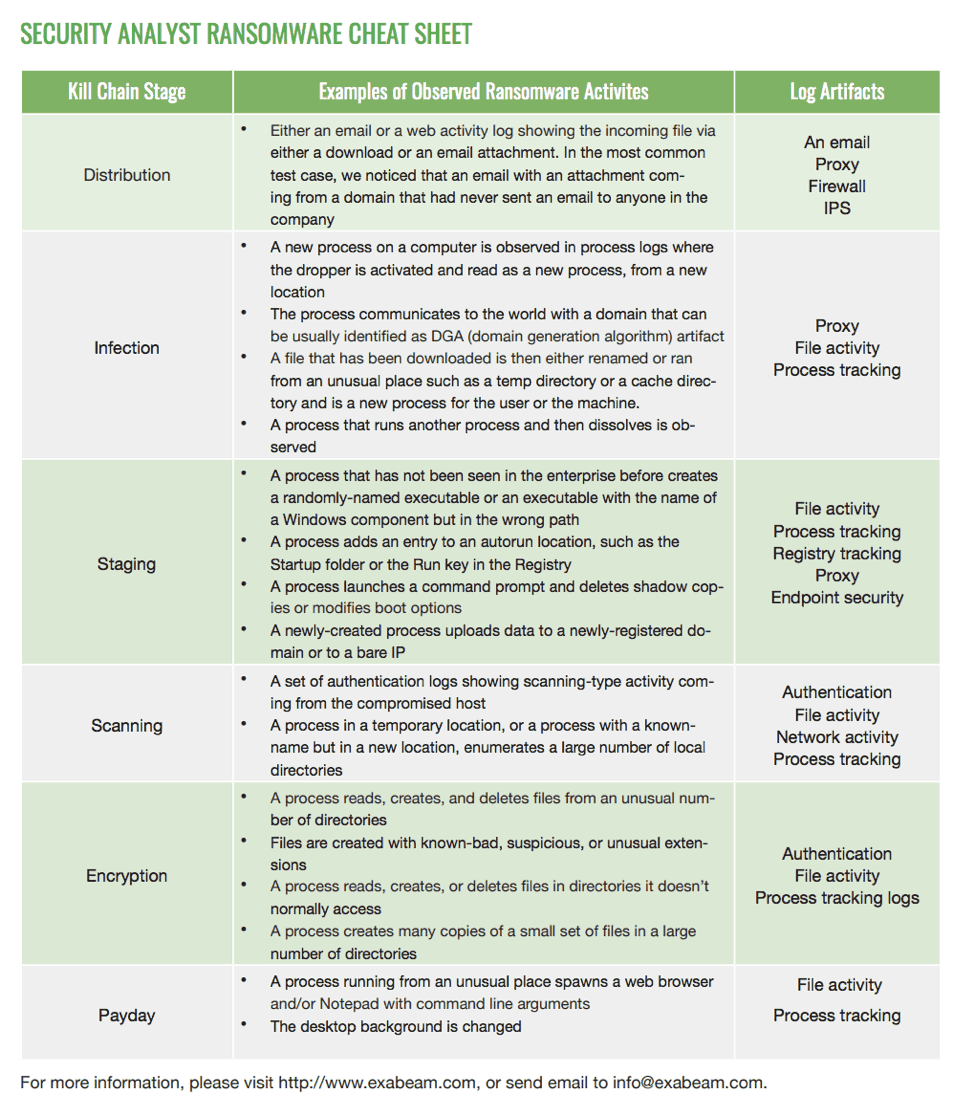
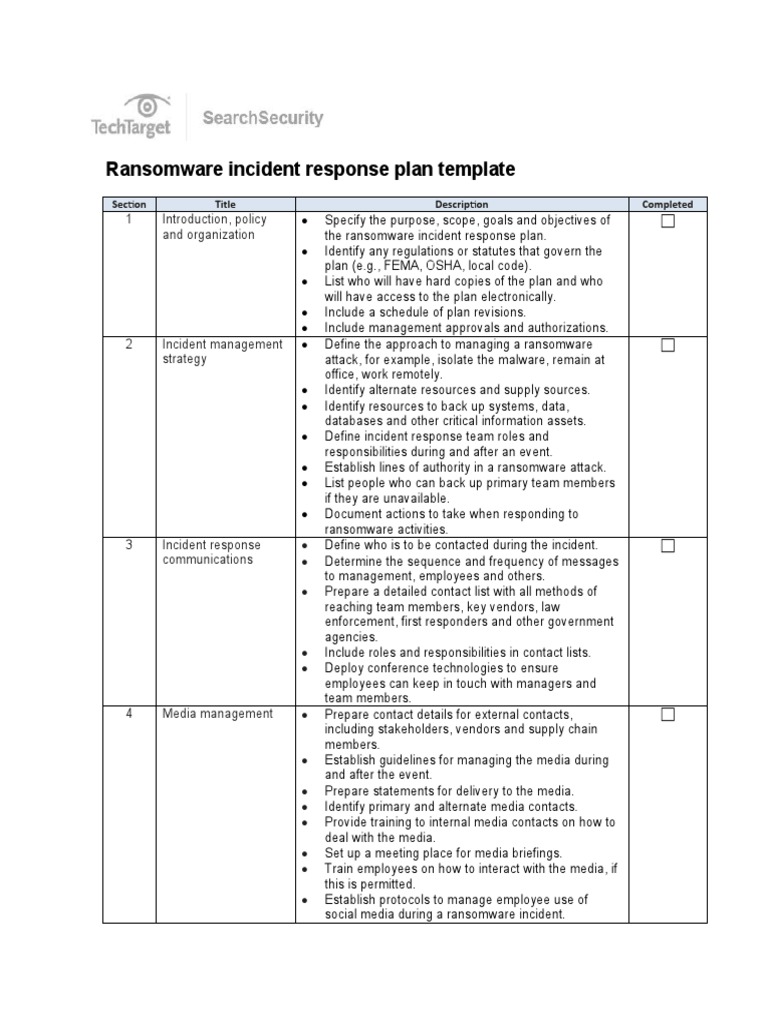
Automatic detection of potential ransomware activity. The workflow is aimed at team leaders who need to coordinate actions through each stage of incident response, from detection to recovery. Read key planning steps, and download a free template to get started. Web on september 21, 2021, the u.s. Nuspire's q2 2023 cyber threat report shows rapid growth of cl0p ransomware gang.
Preventing Ransomware What Your Business Needs To Know
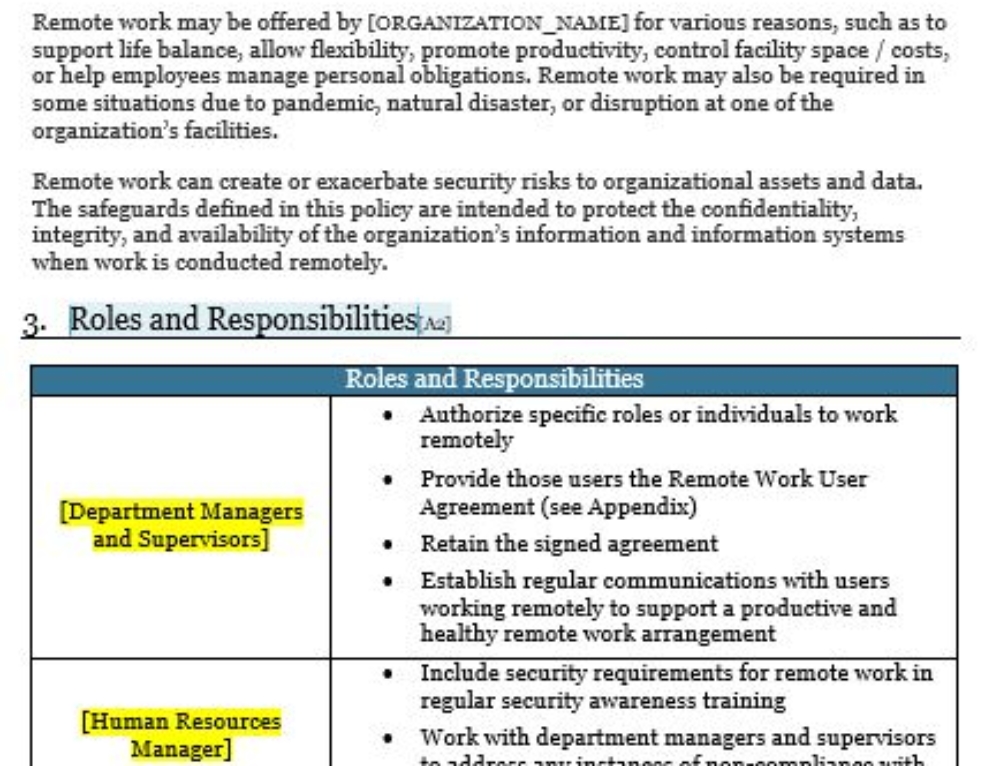
This includes protecting data and devices from ransomware and being ready to respond to any ransomware attacks that succeed. Web risk management implement security measures sufficient to reduce identified threats and vulnerabilities to a reasonable and appropriate level access controls ensure access rights granted are not excessive business associate agreements define processes, including responsibilities, to prevent, manage and report security.
Overview of threat protection scenario Microsoft Docs
The department of the treasury’s office of foreign assets control’s (“ofac”) for the first time designated a virtual currency exchange for facilitating financial. Sign up for free at becyberready.com. Web so you may need a ransomware policy. Automatic detection of potential ransomware activity. Ransomware is a component in nearly 25% of all breaches, according to verizon's 2023 data breach investigations.
Incident Response Services Security Risk LBMC
Quick and easy to customize. Web ransomware is a type of malicious software cyber actors use to deny access to systems or data. Here are additional resources from nist and partner federal agencies to help you protect against and respond to ransomware attacks : The playbook defines key stakeholders, processes, policies & prevention plans to defend your organization. Nuspire's q2.
Ransomware Negotiation Tips LMG Security
After the initial infection, the ransomware attempts to spread to shared storage drives and other accessible systems. Department of the treasury announced a set of actions designed to counter ransomware, principally by discouraging ransomware payments. The playbook defines key stakeholders, processes, policies & prevention plans to defend your organization. The estimated cost of restoration, the likelihood of successful restoration whether.
A Closer Look at Ransomware Attacks Why They Still Work
The workflow is aimed at team leaders who need to coordinate actions through each stage of incident response, from detection to recovery. After the initial infection, the ransomware attempts to spread to shared storage drives and other accessible systems. Department of the treasury announced a set of actions designed to counter ransomware, principally by discouraging ransomware payments. Unique slides with.
Ransomware Incident Response Plan Template PDF Ransomware
Web the policy should specify the parameters to be considered, including the cost of the ransom vs. Web on september 21, 2021, the u.s. Web 21 hours agothe infamous blackcat ransomware group, also known as alphv, has claimed responsibility for an attack on watchmakers seiko, which happened earlier this month. Web instructions and templates to help you create your own.
This includes protecting data and devices from ransomware and being ready to respond to any ransomware attacks that succeed. Web 21 hours agothe infamous blackcat ransomware group, also known as alphv, has claimed responsibility for an attack on watchmakers seiko, which happened earlier this month. Ransomware prevention best practices be prepared refer to the best practices and references below to help manage the risk posed by ransomware and support your organization’s coordinated and efficient response to a ransomware incident. Web ransomware is a form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Nuspire's q2 2023 cyber threat report shows rapid growth of cl0p ransomware gang. Web ransomware is a type of malicious software cyber actors use to deny access to systems or data. Ransomware extortion and destructive attacks only work when all legitimate access to. To read about real examples of how companies and municipalities responded to a ransomware attack, please visit cyber readiness news. The estimated cost of restoration, the likelihood of successful restoration whether the ransom is paid or not, regulatory implications (see below), and the criticality of the data. Microsoft on thursday disclosed that it found a new version of the blackcat ransomware (aka alphv and noberus) that embeds tools like impacket and remcom to facilitate lateral movement and remote code execution. Web so you may need a ransomware policy. Web new blackcat ransomware variant adopts advanced impacket and remcom tools. The malicious cyber actor holds systems or data hostage until the ransom is paid. Malicious actors then demand ransom in exchange for decryption. Web create the policy. Here are nist resources that can help you with ransomware protection and response. Want to protect yourself from emerging. Automatic detection of potential ransomware activity. Web get ahead of your 2023 security goals. Web risk management implement security measures sufficient to reduce identified threats and vulnerabilities to a reasonable and appropriate level access controls ensure access rights granted are not excessive business associate agreements define processes, including responsibilities, to prevent, manage and report security incidents and breaches